Welcome to the first day of Pwn2Own Vancouver 2024! We have two amazing days of research planned, including every browser, SharePoint, and Tesla. We’ll be updating this blog in real time as results become available. We have a full schedule of attempts today, so stay tuned! All times are Pacific Daylight Time (GMT -7:00).
And we’re done with Day One of Pwn2Own Vancouver 2024. We awarded $732,500 USD for 19 unique 0-days. See below for the details of each event. Here are the Master of Pwn standings after the first day:
SUCCESS - AbdulAziz Hariri of Haboob SA was able to execute their code execution attack against Adobe Reader. He combined an an API Restriction Bypass and a Command Injection bug. He earns himself $50,000 and 5 Master of Pwn points.
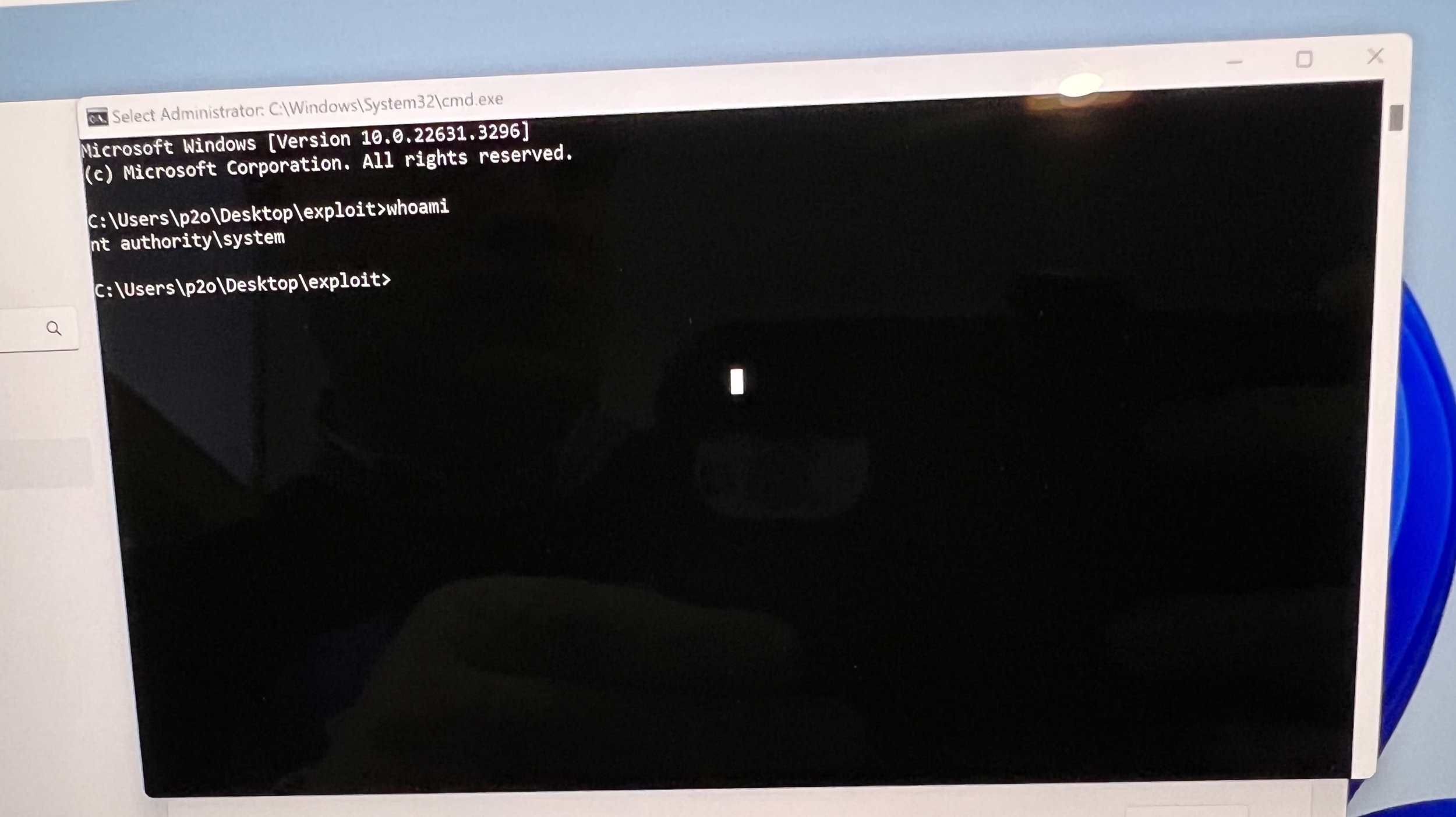
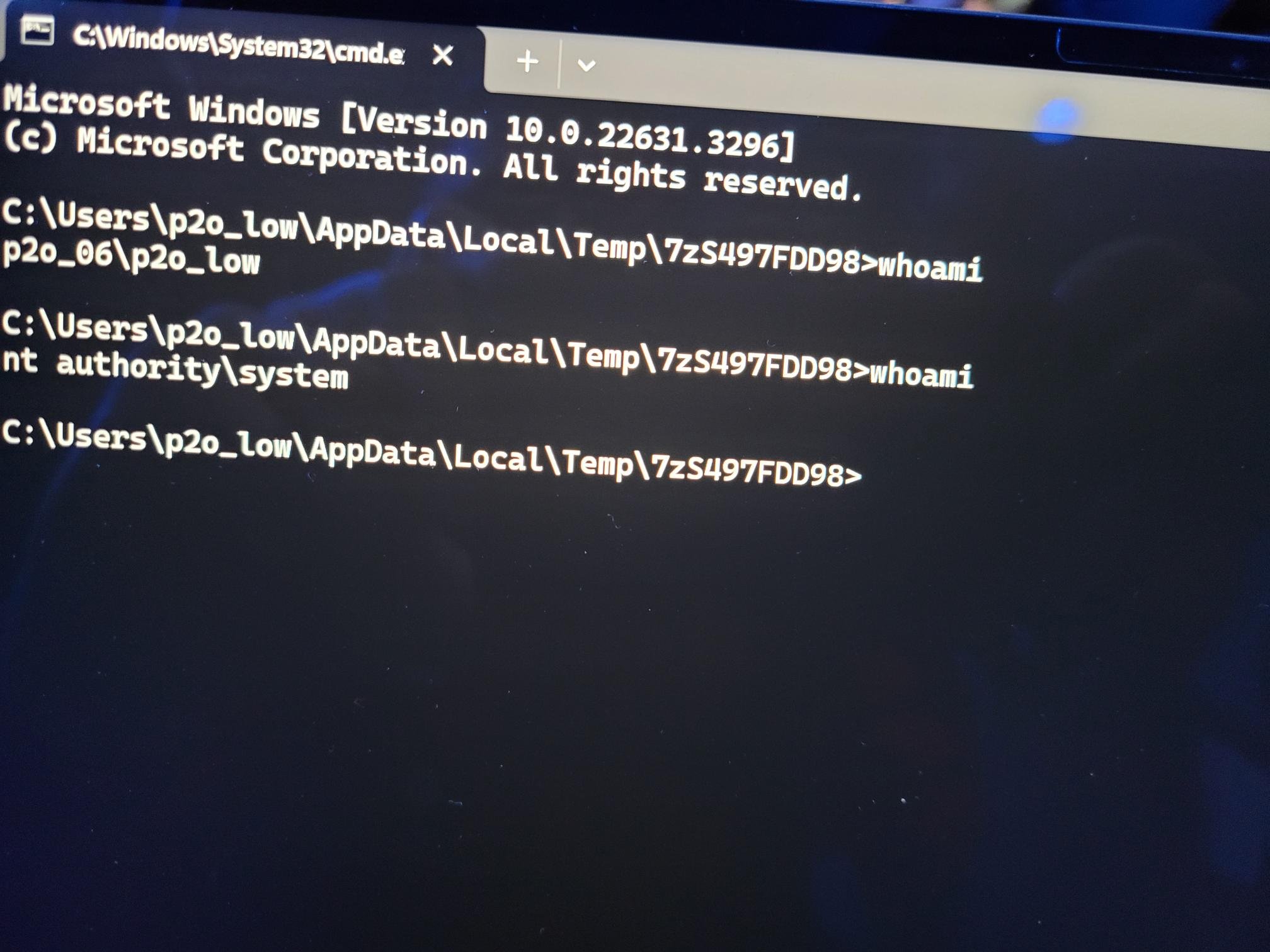
SUCCESS - The DEVCORE Research Team was able to execute their LPE attack against Windows 11. They combined a couple of bugs, including a somewhat risky TOCTOU race condition. They earn $30,000 and 3 Master of Pwn points.
FAILURE - The Starlabs SG team was unable to get their exploit of Microsoft SharePoint working within the time allotted.
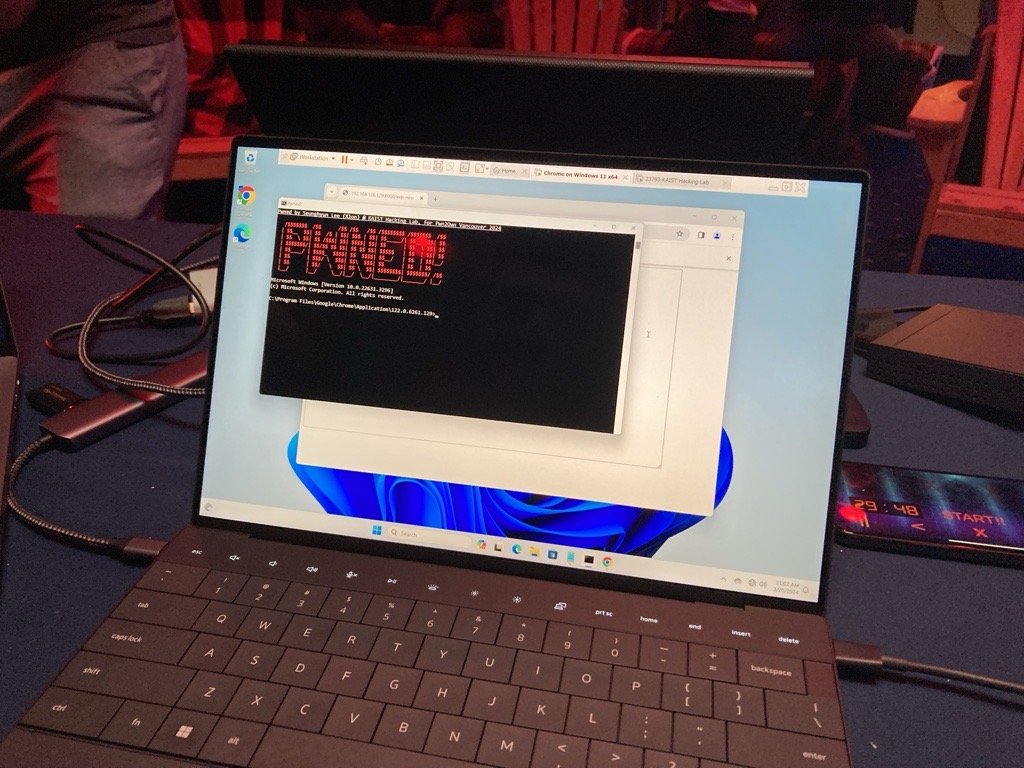
SUCCESS - Seunghyun Lee (@0x10n) of KAIST Hacking Lab was able to execute their exploit of the Google Chrome web browser using a single UAF bug. They earn $60,000 and 6 Master of Pwn points.
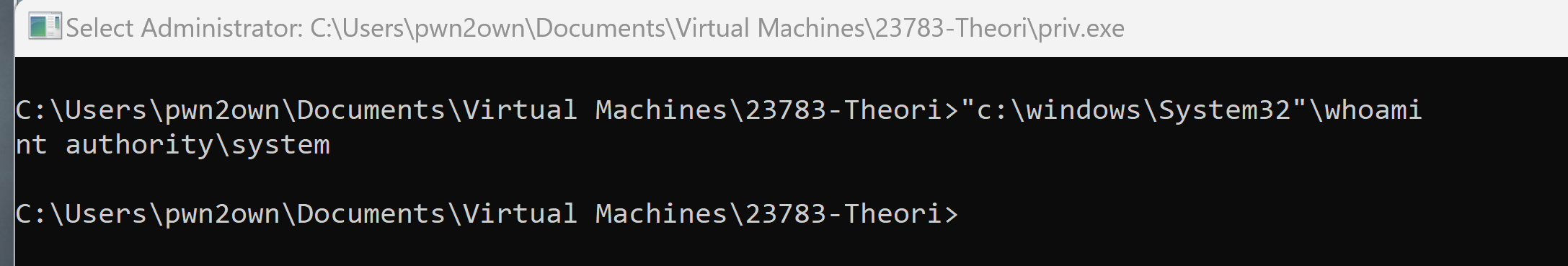
SUCCESS - Gwangun Jung (@pr0ln) and Junoh Lee (@bbbig12) from Theori (@theori_io) combined an uninitiallized variable bug, a UAF, and a heap-based buffer overflow to escape VMware Workstation and then execute code as SYSTEM on the host Windows OS. This impressive feat earns them $130,000 and 13 Master of Pwn points.
BUG COLLISION - The DEVCORE Team was able to execute their LPE attack against Ubuntu Linux. However, the bug they used was previously known. They still earn $10,000 and 1 Master of Pwn points.
SUCCESS - Bruno PUJOS and Corentin BAYET from REverse Tactics (@Reverse_Tactics) combined two Oracle VirtualBox bugs - including a buffer overflow - along with a Windows UAF to escape the guest OS and execute code as SYSTEM on the host OS. This fantastic research earns them $90,000 and 9 Master of Pwn points.
SUCCESS - The Synacktiv (@synacktiv) team used a single integer overflow to exploit the Tesla ECU with Vehicle (VEH) CAN BUS Control. The win $200,000, 20 Master of Pwn points, and a new Tesla Model 3 (their second!).
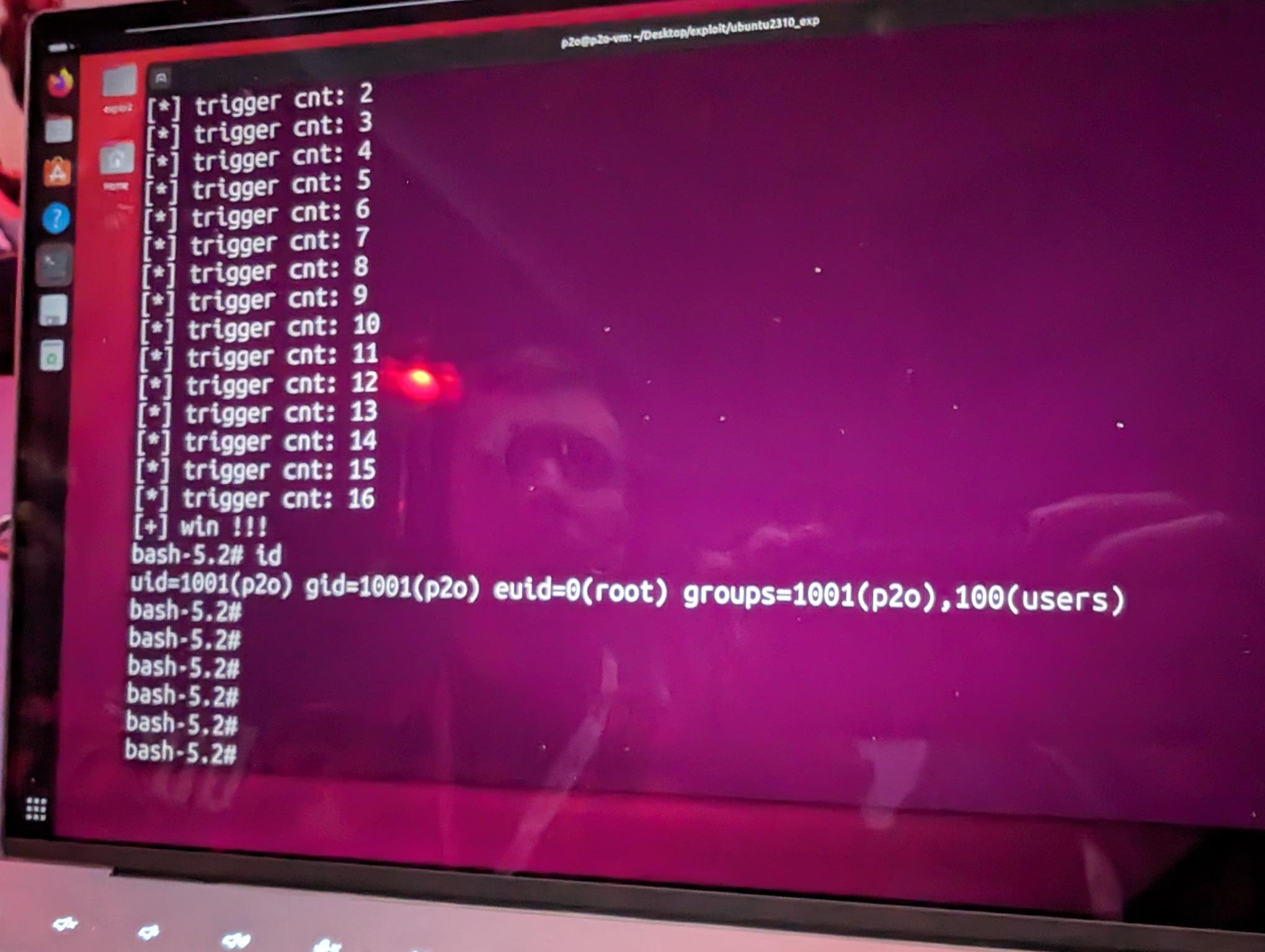
SUCCESS - Kyle Zeng from ASU SEFCOM used an ever tricky race condition to escalate privileges on Ubuntu Linux desktop. This earns him him $20,000 and 20 Master of Pwn points.
SUCCESS - Cody Gallagher used a single OOB Write bug to exploit Oracle VirtualBox. His first ever Pwn2Own attempt results in him winning $20,000 (second round win) and 4 Master of Pwn points.
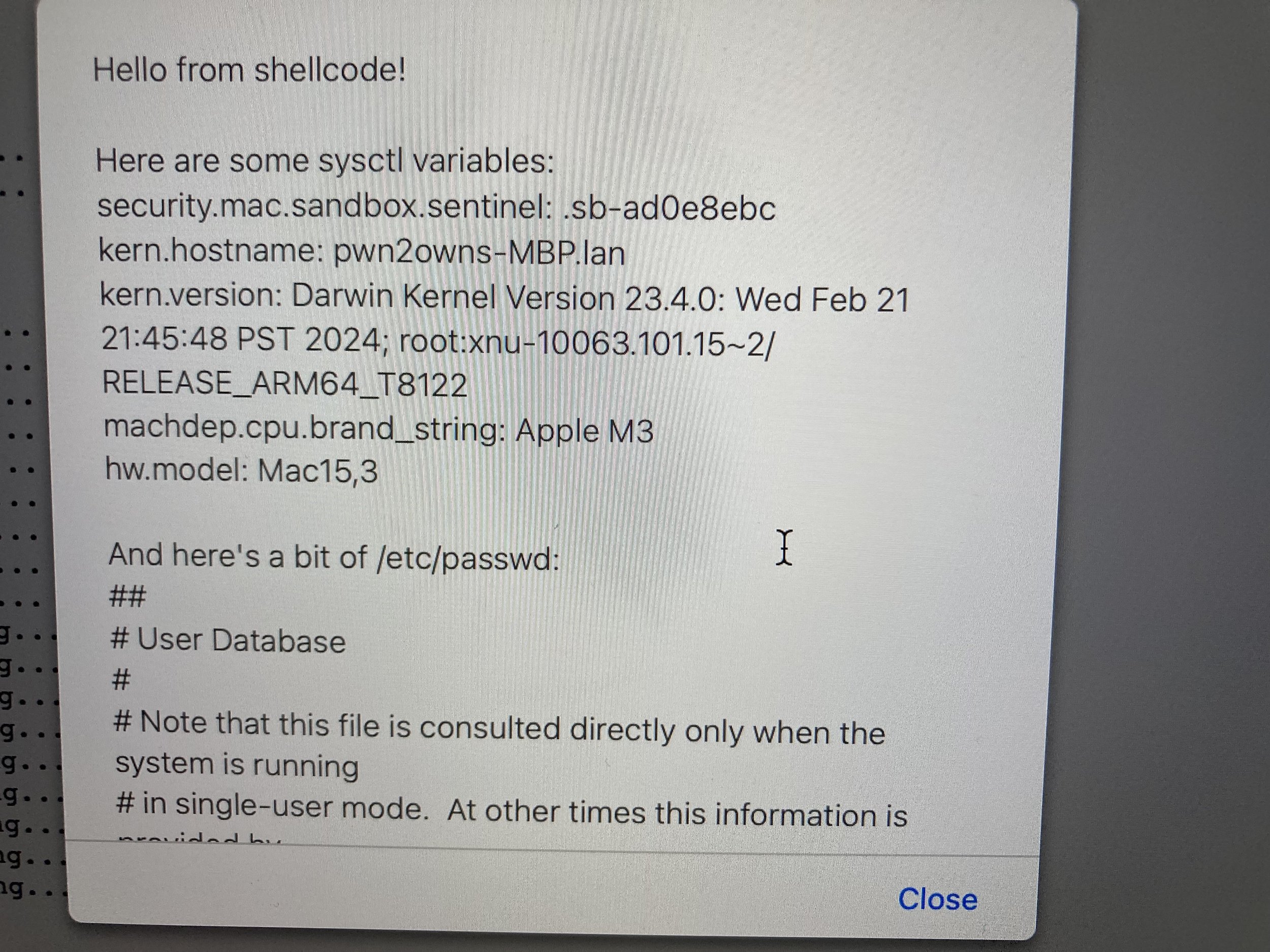
SUCCESS - Manfred Paul (@_manfp) gets RCE on the Apple Safari browser with an integer underflow bug plus a PAC bypass using a weakness in Apple Safari. He wins himself $60,000 and 6 Master of Pwn points.
FAILURE - STAR Labs SG could not get their exploit of VMware ESXi working within the time allotted.
SUCCESS - Dungdm (@_piers2) of Viettel Cyber Security used two bugs, including the ever-risky race condition, to exploit Oracle VirtualBox. As a round 3 winner, they receive $20,000 and 4 Master of Pwn points.
SUCCESS - Manfred Paul (@_manfp) executed a double-tap exploit on both Chrome and Edge browsers with the rare CWE-1284 Improper Validation of Specified Quantity in Input. His Round 2 win earns him $42,500 and 15 Master of Pwn points.
That’s a wrap on Day One of Pwn2Own Vancouver 2024. We awarded $732,500 for 19 unique bugs. Tune in tomorrow to see if Synacktive can hold on to their Master of Pwn lead or if Manfred Paul is able to overtake them.